CORS Errors Explained: A Visual Guide to Web Security
Ever hit a wall trying to get your web app to talk to an API? You fire off a request, feeling confident, and then — BAM! — a cryptic error message pops up in your console. It probably mentions something about “Access-Control-Allow-Origin.” Sound familiar?
That, my friend, is a CORS error. Don’t worry, you are absolutely not alone. Many developers, especially beginners, stumble here. Today, we’re going to get CORS errors explained in plain English. You will understand what’s happening and how to fix it.
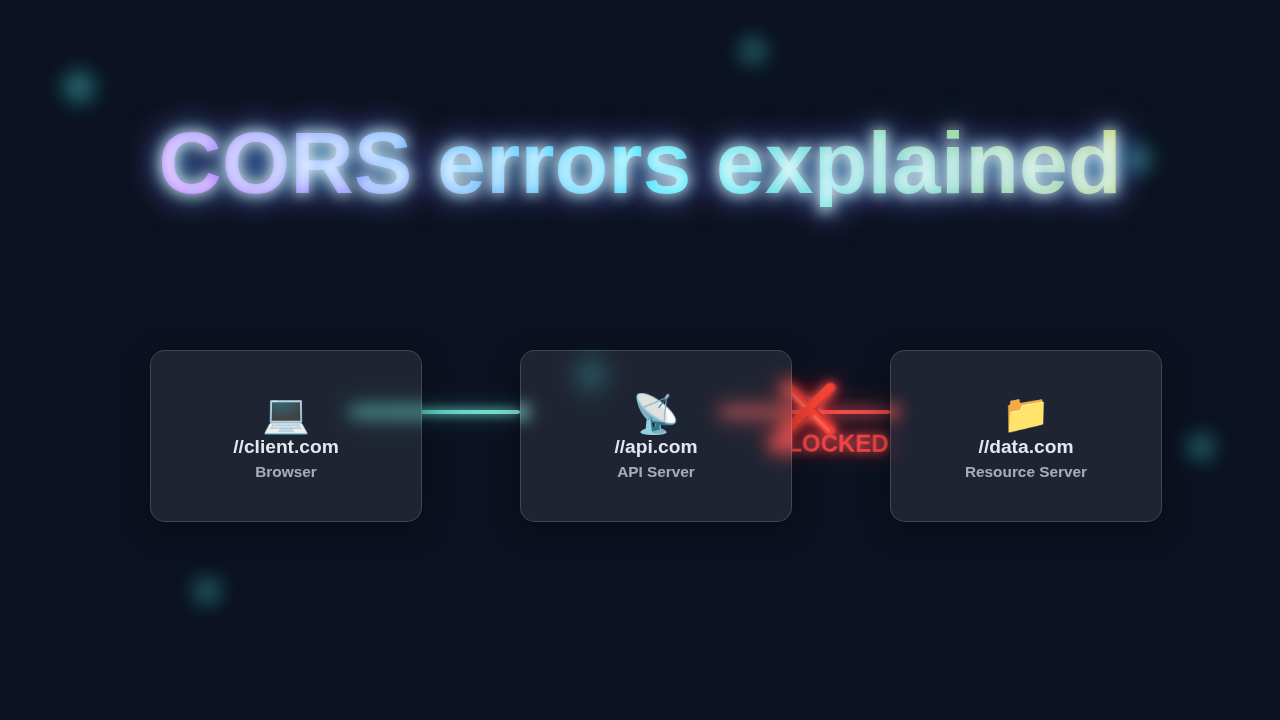
Here’s the thing about the internet: it’s a bustling city. You have different websites, different servers, all living in their own neighborhoods. When your browser tries to reach out from one neighborhood (your website) to another (an API server), it needs permission. CORS, or Cross-Origin Resource Sharing, is that permission system.
Without it, any website could potentially snatch data from any other website. Imagine your banking site’s data being readable by a sketchy third-party ad server. Not good, right? So, CORS is a vital security feature built right into your web browser. It keeps everyone safe, even if it feels like a hurdle sometimes.
What Are CORS Errors Explained?
Let’s dive into some practical tips. These will help you grasp the core concepts. Furthermore, you will learn how to tackle those pesky errors head-on.
-
Understand the Core Concept of CORS
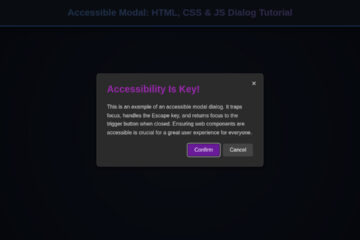
CORS is your browser’s security guard. It prevents malicious websites from making requests to other domains without explicit permission. When your frontend (running on one domain) tries to fetch resources from a backend API (on another domain), the browser steps in. It checks if the backend server has given explicit consent for your frontend’s domain to access its resources.
For example, you are building a React app on
my-cool-app.com. It needs data from an API atdata-provider.com. Your browser will send the request. However, it will also check ifdata-provider.comhas said, “Yes,my-cool-app.comis allowed to talk to me.” If not, the browser blocks the response. It does not even let your JavaScript see the data. -
Why Does This Even Exist? (Security!)
The Same-Origin Policy (SOP) is the fundamental rule here. It dictates that a web page can only request resources from the same origin (same protocol, host, and port) it originated from. CORS is essentially a controlled relaxation of this strict policy. It allows you to opt-in to cross-origin requests securely.
Imagine your browser as a bouncer at a club. The club’s rule is “No outside food or drinks.” That’s SOP. However, if the club owner says, “Okay, Bob from the pizza shop next door can bring in pizzas,” that’s CORS. Bob (your frontend) gets a special pass to interact with the club (the backend API).
CORS isn’t a bug; it’s a feature. It protects your users from data theft and malicious attacks across different websites.
-
The ‘Origin’ is Key
Your origin is defined by three parts: the protocol, the host, and the port. If any of these differ, you have a different origin. For instance,
http://example.com,https://example.com,http://sub.example.com, andhttp://example.com:8080are all distinct origins.Consider your development environment. You might be running your frontend on
http://localhost:3000. Your backend API, meanwhile, is onhttp://localhost:5000. These are different origins because their port numbers differ. The browser sees them as separate. Therefore, it applies CORS rules. This is often where your first React State vs Props app runs into its first CORS issues! -
Simple Requests vs. Preflight Requests
Not all cross-origin requests are treated equally. Some are “simple requests.” These include GET, HEAD, and POST requests with specific content types. The browser sends these directly. Other, more complex requests trigger a “preflight request.”
A preflight request is an OPTIONS request. Your browser sends it automatically before the actual request. It asks the server, “Hey, are you cool with me sending a DELETE request with a custom header from this origin?” The server then replies with headers indicating its allowed methods, headers, and origins. If the server says yes, the browser sends the real request. Otherwise, it blocks it immediately. You can read more about HTTP access control headers on CSS-Tricks.
-
Common CORS Error Messages and What They Mean
You will often see messages like “No ‘Access-Control-Allow-Origin’ header is present on the requested resource.” This means the server didn’t explicitly grant permission. Another common one is “Response to preflight request doesn’t pass access control check.” This points to an issue with the OPTIONS request response.
Think of it as trying to enter a private club. If the bouncer says, “Your name’s not on the list!” (no ‘Access-Control-Allow-Origin’ header), you’re denied. If you try to enter with a strange outfit, and the bouncer asks, “What’s that? You can’t wear that here!” (preflight failure), you also won’t get in. Both scenarios result in you being unable to access the club’s resources.
-
How to Fix CORS on the Server Side
Most CORS fixes happen on the server. You, as the backend developer, need to configure your server. It must send the correct `Access-Control-Allow-Origin` header in its responses. This header tells browsers which origins are permitted to access the resource. You can specify a single origin, multiple origins, or even `*` (wildcard) for all origins (though use `*` with caution in production).
For example, in a Node.js Express application, you might add middleware. This middleware sets the `Access-Control-Allow-Origin` header to
http://localhost:3000orhttps://your-frontend-domain.com. This process is similar for Python frameworks or other backend technologies. It often involves a decorator or a configuration setting, much like how you would configure Python Decorators for specific functions. -
Client-Side Proxies (For Devs Only!)
During development, you might use a proxy. This allows your frontend to route requests through its own server. The proxy then forwards the request to the actual API. Because the request originates from the same server as your frontend, the browser doesn’t see a cross-origin request. This bypasses CORS issues locally.
Picture this: you want to order food from a new restaurant. It only accepts orders from within a certain district. You, living outside that district, ask a friend who lives inside it to order for you. Your friend acts as a proxy. The restaurant sees the order coming from your friend’s address (a permitted origin). This is a great trick for local testing, but never rely on it for production.
Remember: fixing CORS on the client-side with proxies is a development hack. Always aim to solve CORS on the server for production applications.
Debugging CORS Errors Explained: Your Bonus Tip
Use your browser’s developer tools! In the Network tab, you can inspect the request and response headers. Look for the `Origin` header in your request. Then, check for `Access-Control-Allow-Origin` in the response from the server. This is often where you find the missing piece of the puzzle. It shows you exactly what your server is, or isn’t, sending back.
CORS Errors Explained: Next Steps
See? CORS errors explained aren’t so scary after all! They are a fundamental part of web security. Understanding them empowers you to build safer, more robust web applications. It’s all about communication and setting the right permissions between your frontend and backend.
Next time you face an `Access-Control-Allow-Origin` error, you will know exactly what to look for. You will understand that your browser is doing its job protecting users. Then you can confidently configure your server to grant the correct permissions. Keep building, keep learning, and you will master these web dev concepts!